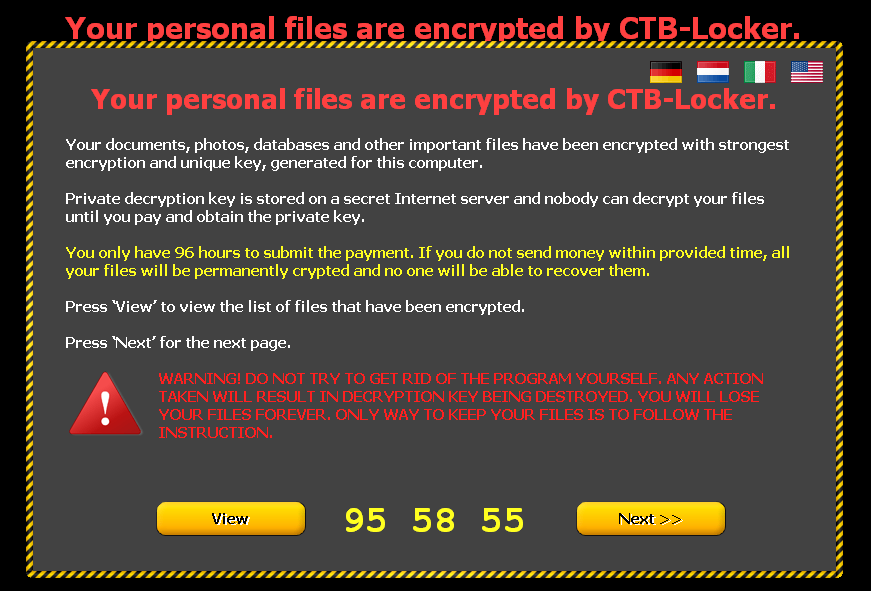
Cryptoviruses make many victims worldwide, it is computer malware that that holds the victim’s data hostage.

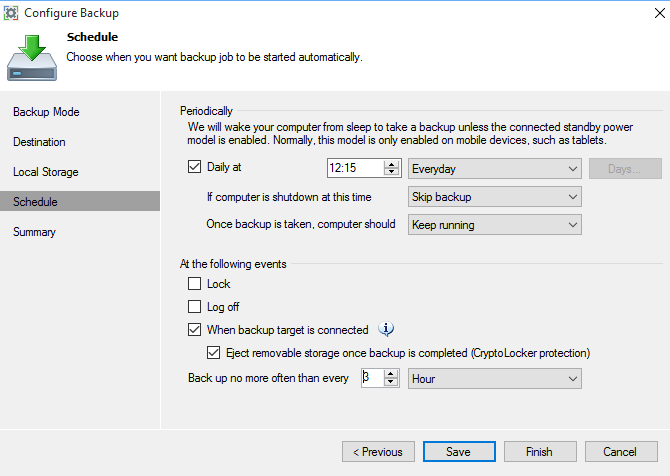
Make a backup with Veeam Endpoint Backup FREE 1.5 (Protection from CryptoLocker for usb)
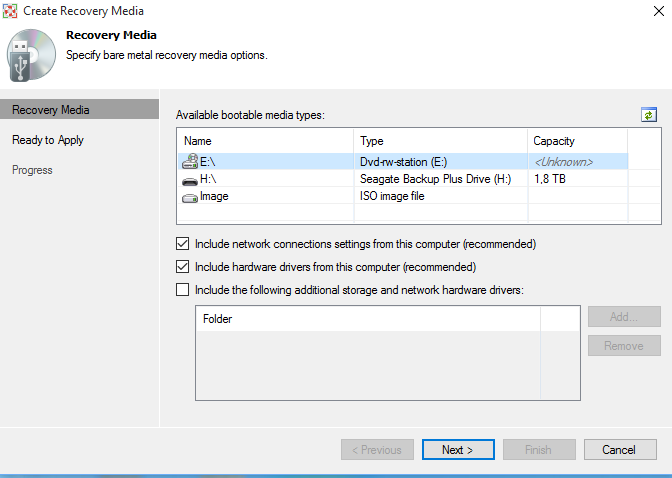
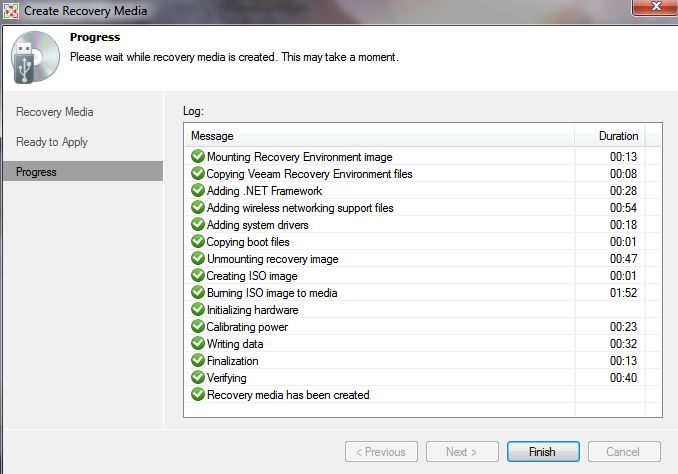
 Bootable recovery media
Bootable recovery media
Veeam Endpoint Backup FREE lets you create a recovery image of your computer on several different kinds of media, including:
- Removable storage devices (e.g., USB flash drives, SD cards, etc.)
- CD/DVD/BD media
- ISO image
The recovery image provides an alternative way to boot your computer. If the OS installed on the computer fails to start for some reason, you can boot the OS from the recovery image and leverage the included recovery tools.
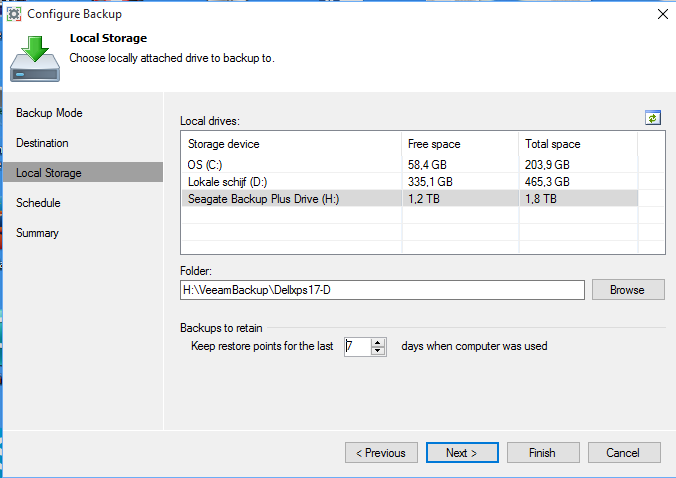
With Veeam you create an image of your installation files and you can define retention periods.
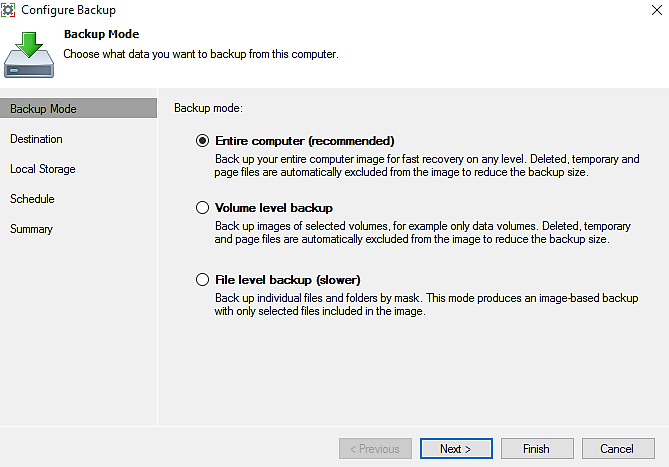
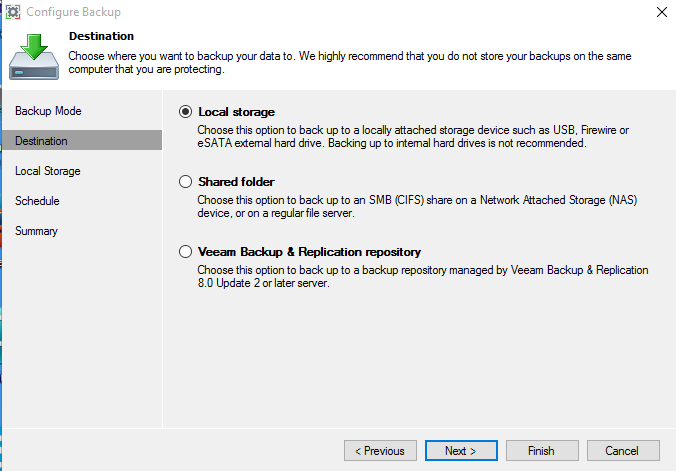
Configuration for the back-up
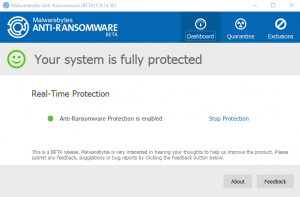
Now you can see that ‘CryptoLocker protection’ is enabled!